Intel confirms remote code execution hole in Intel CPUs since 2008
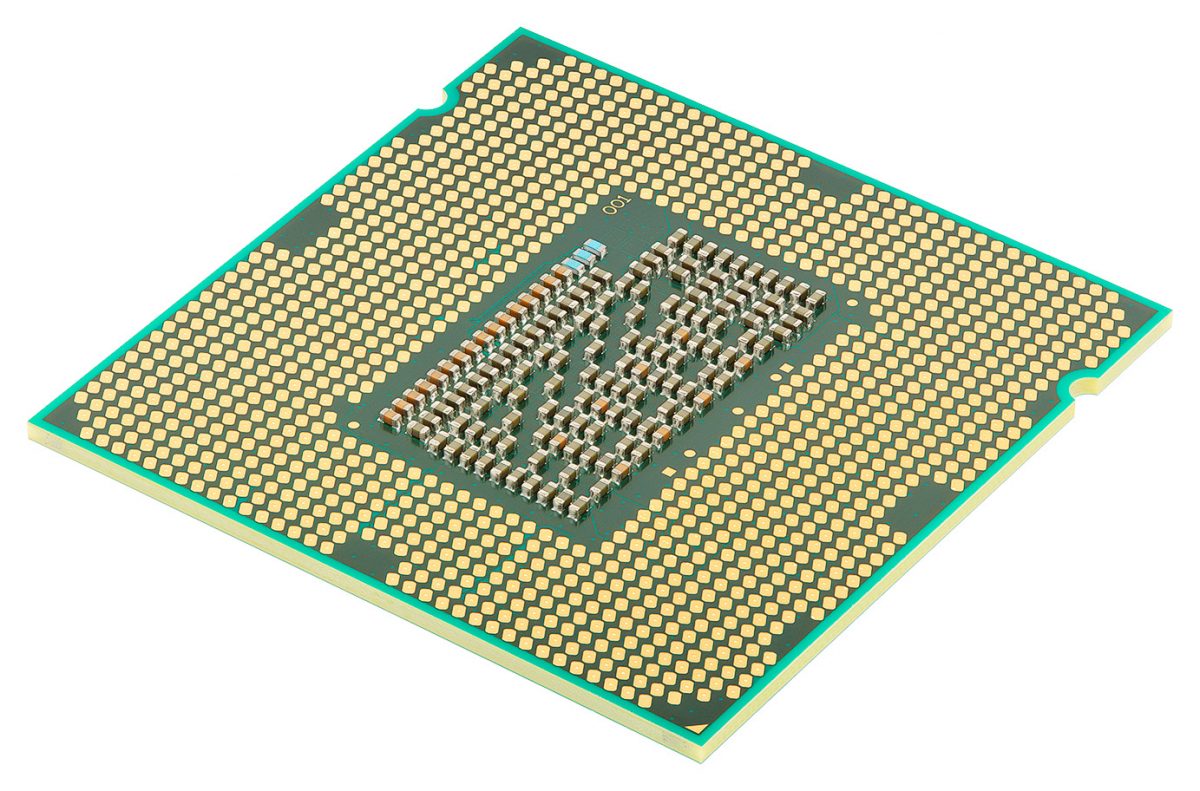
According to security researchers, media, and now Intel themselves, a security hole allowing remote code execution (RCE) has been present in Intel CPUs since 2008. The exploit was usable on Intel Active Management Technology (AMT), Small Business Technology (SBT), and Standard Manageability (SM). Those are present in most every computer with an Intel CPU from the last ten years, and allowed for remote execution of code on the CPU. Charlie Demerjian at SemiAccurate first reported the news earlier today:
“The short version is that every Intel platform with AMT, ISM, and SBT from Nehalem in 2008 to Kaby Lake in 2017 has a remotely exploitable security hole in the ME (Management Engine) not CPU firmware.”
Intel confirms escalation of privilege vulnerability
SemiAccurate has known about the exploit for over five years before releasing the news earlier today. SemiAccurate, along with many others such as Richard Stallman, have been warning that something like this could happen and likely had happened already. Today, May 1st, 2017, we have confirmation.
The issue was confirmed with a security advisory later in the day while thanking Maksim Malyutin from Embedi. They have released a firmware fix and it will be distributed asap. The CPU maker admitted that the vulnerability allowed for “an unprivileged attacker to gain control of the manageability features provided by these products.” The manageability features allow all sorts of shenanigans. Intel confirmed to SemiAccurate that AMT can be used to “bare metal image a dead machine over a cellular connection.” Needless to say, if they can do that – they can do anything.
The security advisory also states that this vulnerability did not/does not exist on consumer PCs, only non-consumer PCs. In the public eye, the veracity of this claim has not been proven. If your computer doesn’t have VPro, then it doesn’t have AMT and isn’t vulnerable. It’s also worth noting that Apple Macs do not use Intel AMT, and thus were not vulnerable.
Like this article? Get notified by email when there is a new article or signup to receive the latest news in the fight for Privacy via the Online Privacy News RSS Feed.
Comments are closed.

This article is wrong on several fronts, the first and foremost being the entirely wrong claim that this affected ALL Intel CPU’s. Simply not so.