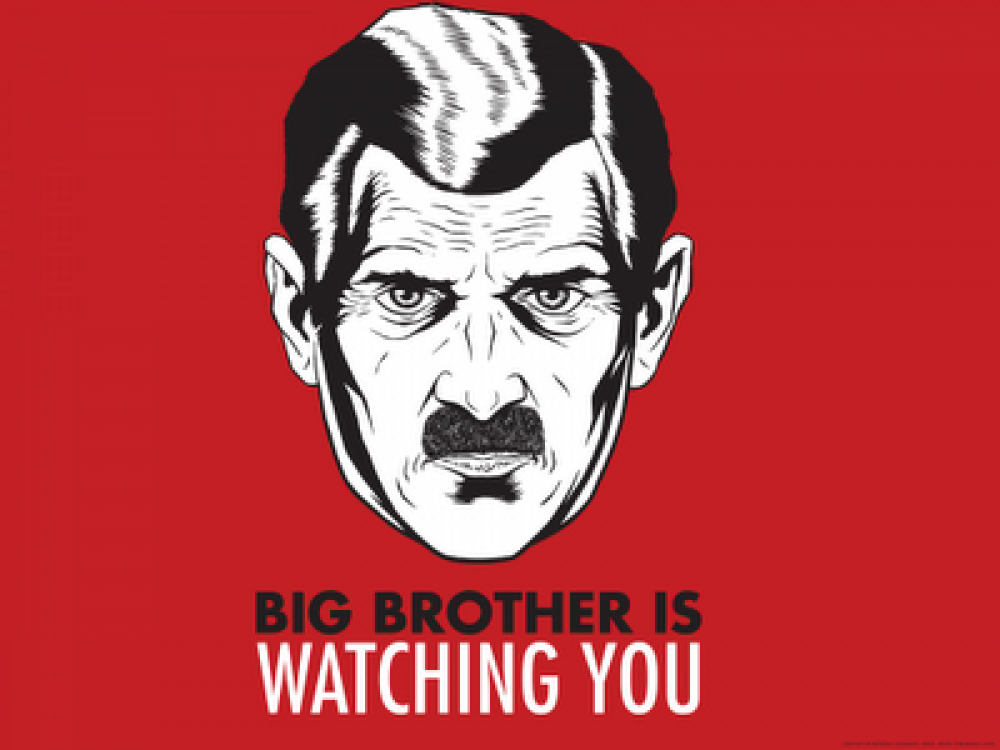
Welcome to the brave new world of workplace surveillance
Here on Privacy News Online, we write a lot about government surveillance and its impact on privacy. Sadly, constant spying has been normalized to such an extent that workplace surveillance is a thriving new business sector that startups and established companies are rushing to serve. For example, InterGuard promises “complete end-user auditing and control”, and says:
“In most businesses, human capital is your most significant cost. While PCs can increase staff productivity, they can also be a great distraction. By recording all PC activity, both on or off network, Sonar helps you maximize employee productivity by ensuring that your resources are focused on work.”
As well as obvious features such as noting every email sent and received, tracking both sides of instant messaging applications, recording social networking activity, monitoring online searches and which Web sites are visited, InterGuard’s Sonar software will watch for pre-defined keywords, sending alerts to managers and taking a screenshot of the relevant moment. In addition, it has a keystroke logger:
“Capture every keystroke typed even if it is deleted. InterGuard keystroke logger feature provides a reader-friendly version of all keystrokes logged along with the raw keylogging activity so you can see every detail.”
And if that is not enough, it also offers continuous screenshots of employee activity, providing:
“Video-style playback of screenshots for programs and websites selected by you. For example, watch an e-mail as it’s being typed and edited instead of just seeing the finished product.”
Teramind offers similar capabilities, plus a few extra ones, including:
“Administrative ability to interact and take control of a user’s desktop in a potential breach situation
Extensive history logs allow past recordings to be searched and retrieved in seconds
Optional audio support for the recording of both sound outputs and inputs, ensuring that all audio coming from speakers and microphones is captured”
Teramind says its software allows “insider risk management”, enabling companies to “Identify which employees are most risky to your organization by analyzing trends in their behavior. Drill down to see which policies they violated. Educate them to prevent future incidents.”
Continuous monitoring of employees inevitably produces huge quantities of information. The ability to automate the analysis of that data is an increasingly important aspect of workplace surveillance tools. For example, Digital Reasoning uses what it calls “cognitive analytics” to spot employees that might be putting a company “at risk”:
“Cognitive computing changes what’s possible, allowing enterprises to truly develop a ‘Know-Your-Employee’ strategy that delivers insights from across the organization with speed and precision. Our cognitive computing based platform, Synthesys monitors all forms of electronic communications – email, chat, phone calls, images, documents and social media, and delivers an entity-centric view of all this valuable data, and intelligently pinpoints employees that are putting the organization at risk.”
Others companies looking to harness artificial intelligence to keep track of employees and spot deeper trends are Dynatrace and Wiretap:
“a cloud security platform that aims to adopt the latest advancements in cognitive computing, artificial intelligence and behavioral analytics to amplify enterprise value by monitoring the social graph (Office 365, Slack, FB workplace). We really believe that we can harness the power of our platform’s insights into human behavior and interactivity to create great value for the enterprise.”
Although the use of increasingly powerful and cost-effective AI solutions is a logical move, it brings with it all the problems that have been discussed on this blog before. For example, AI-based systems often come with their own set of assumptions about acceptable behavior in the workplace, which may not be applicable in every company. Similarly, the black-box approach to employee monitoring makes it hard for people to challenge criticism or the termination of their contract.
The law on workplace surveillance varies considerably. In the US, for example, according to the Privacy Rights Clearinghouse:
“Since the employer owns the computer network and the terminals, he or she is free to use them to monitor employees. Employees are given some protection from computer and other forms of electronic monitoring under certain circumstances. Union contracts, for example, may limit the employer’s right to monitor. Also, public sector employees may have some minimal rights under the United States Constitution, in particular the Fourth Amendment which safeguards against unreasonable search and seizure.”
The situation in the EU is less clear and still rather fluid. An important judgment in the European Court of Human rights ruled that companies can monitor their employees’ email, but only if the latter are notified in advance. In Germany, a court said that evidence collected by a company using keystroke-tracking software could not be used to fire an employee, because such surveillance violated workers’ personal rights. In the UK, by contrast, employers are allowed to monitor the activities of workers in many situations, subject to certain conditions.
Even in jurisdictions and situations where workplace surveillance is legal, there are two key problems with its routine deployment. The first is that employees can try – often successfully – to circumvent monitoring in various ways. An article in the Financial Times last year mentioned cases of drivers who plug cheap GPS jammers from China into the cigarette lighter slots in their vehicles in order to confuse their companies’ tracking systems. Similarly, according to the FT, some workers strap their employer-provided Fitbit movement monitors on to their dogs to boost their activity levels for the day.
The other problem is more subtle and arguably more profound. The use of pervasive monitoring systems to ensure that employees are working hard all the time on their allotted tasks sends a clear message: that they are not trusted to work on their own, and that any attempt to take the initiative by deviating from the required work will be logged and possibly punished. Spying on workers may ensure that they work obediently, but it can also lead to the best of them leaving and finding jobs elsewhere – probably with an employer who respects their privacy, and trusts them to work well without constant surveillance.
Featured image by Sstrobeck23.
