Active 4G LTE vulnerability allows hackers to eavesdrop on conversations, read texts, and track your smartphone location
Zhang Wanqiao, a Chinese researcher from Qihoo 360 has demonstrated an active 4G LTE vulnerability that allows any dedicated attacker to intercept your calls and texts as well as track your location. The hack was demo’d yesterday at the Ruxcon security conference in Melbourne, Australia. This 4G vulnerability is currently exploitable on any LTE network and is based off a little-known “fail-safe” that is supposed to only be used during emergencies, such as natural disasters, when individual cell phone towers are likely to become overloaded and redirection may be necessary. However, there might be a simpler reason as to why this 4G vulnerability is still active and there are no plans to fix it… One word: “Stingray.”
Your smartphone conversations, texts, and location aren’t safe over 4G LTE
Interestingly enough, the 3GPP, the organization in charge of setting mobile data network standards and enforcing them, also acknowledged the issue in 2006 but chose to do nothing about it. Researchers brought up this vulnerability to the world in 2015 in a paper titled: Practical attacks against privacy and availability in 4G/LTE mobile communication systems. That same year, the ACLU managed to obtain documents that described the stingray surveillance device had identical functionalities. In the following year, Zhang Wanqiao of Qihoo 360 extended the practical attack described by the initial researchers and presented on it at DEFCON 24 in August of 2016. Now, at Ruxcon in October of 2016, the attack has been demonstrated and been proven to work on all LTE networks with readily available gear.
At first, Zhang only demonstrated the attack on TDD-LTE networks that operated in Britain, the United States, and Australia; however, Zhang has since confirmed with The Register that this attack is currently viable on any LTE network in the world. It is worth pointing out that this attack works by downgrading your LTE connection to a 3G connection and then finally to an un-secure 2G connection and then exploiting known vulnerabilities there. It’s worth pointing out that this vulnerability might not have been patched because it may have something to do with a surveillance technique that is actively used by law enforcement or intelligence agents in areas without active cooperation of local law enforcement: the highly controversial stingray or IMSI catcher device. While the exact specifics of how stingray tracking devices operate are still unclear, many people have started to draw similarities and differences between that revealed technology and recent research revelations.
How can you protect yourself from being tracked while using 4G?
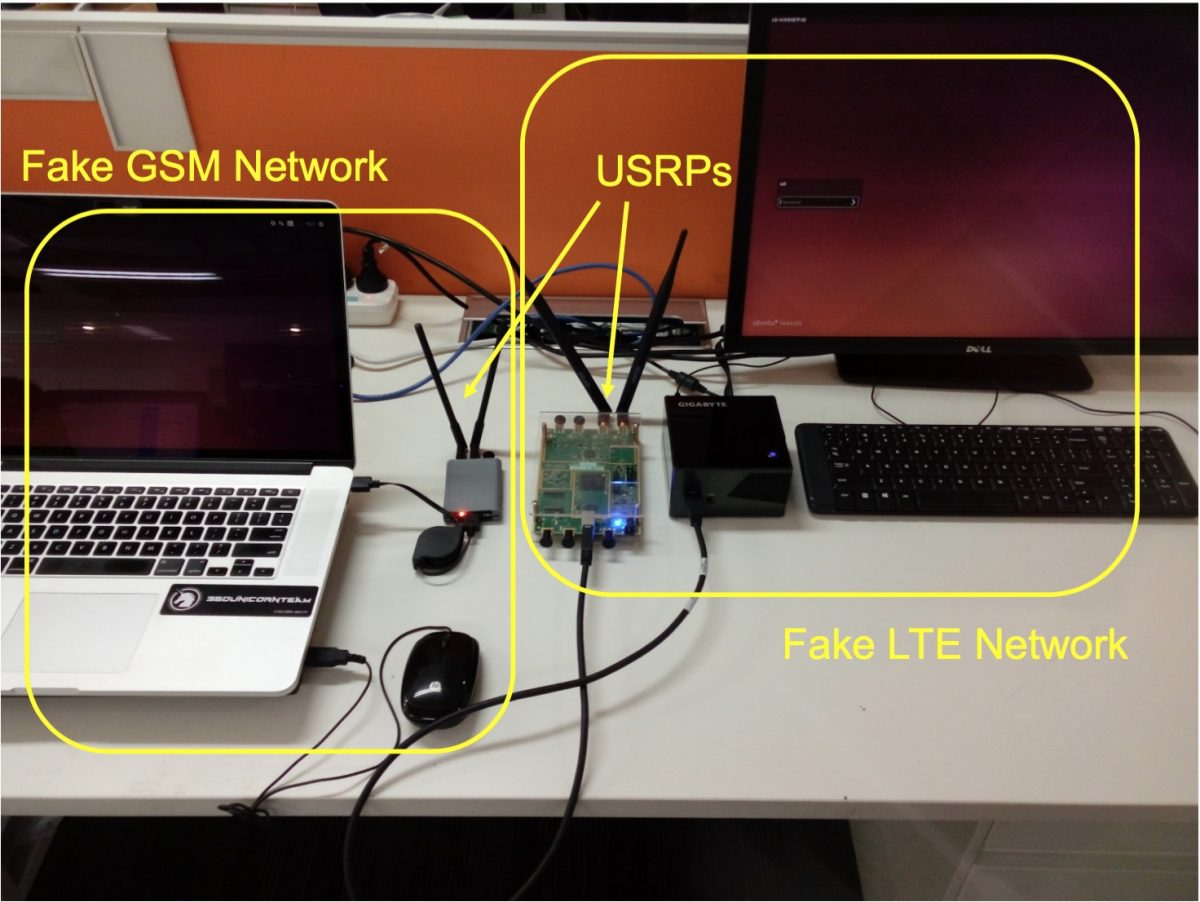
In essence, the attack combines a “personal stingray” (works on GSM which is more commonly known as 2G) and a known vulnerability in 4G and 3G that allows fake LTE towers to force a downgrade all the way down to 2G. Using a VPN that utilizes OpenVPN and its TLS protocol will keep your conversations encrypted even in the face of such an attacker; however, older VPN connection methods such as PPTP/L2TP/SOCKS, you could still be vulnerable, though. Since the attack involves readily available hardware and open source software, any dedicated attacker could be using this against your smartphone at this moment. As the 3GPP has shown, after 10 years, there aren’t any plans to fix this 4G LTE vulnerability.
Featured image from DEFCON.
Comments are closed.

Just write an app that uses the OpenCellID database that constantly polls off of that, whilst running real time scans on area cell towers, and what you connect to. If there is an anomaly that pops up that is not on the map, then chances are it is a fed… That’s what I did…. Cell towers do not just “pop up” overnight. There is a process… VERY LONG… To get one put up… This insures that all data is updated nationwide, and people stay safe from the 3rd world nation state police still trying to keep up the facad.
One thing I’m a bit unclear about: does anyone know if this is GSM only? The above isn’t very specific. I get the impression the vulnerability is in how the systems work in general and thus would work on CDMA as well, but I’m not really quite clear on how true this is. Although, as I say this, I’m now on a GSM network and finally free of that horrid Verizon disservice.