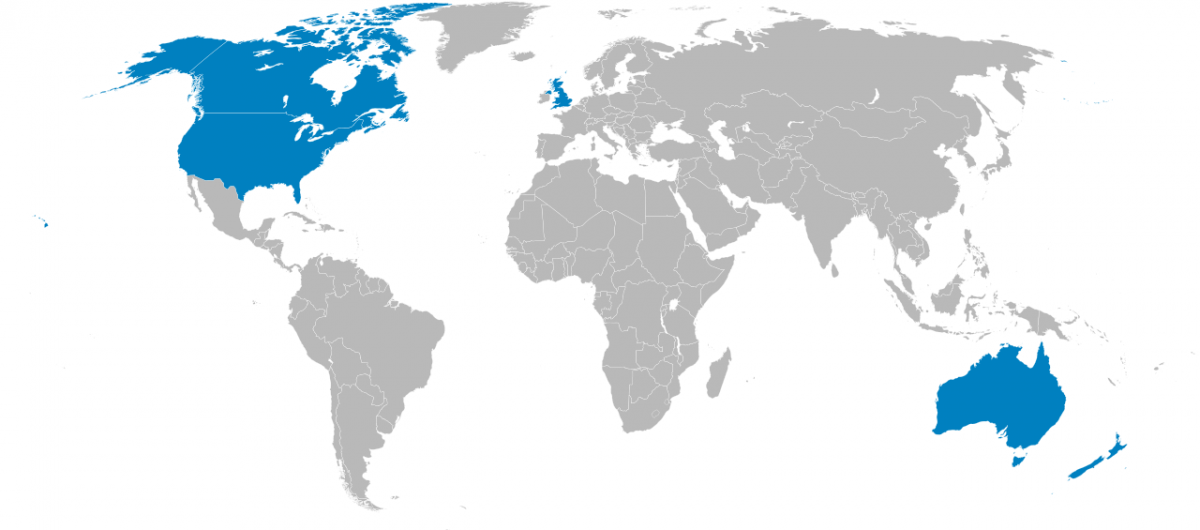
UK, US, Australia, Canada and New Zealand meet to discuss the “ghost protocol” aka built in encryption backdoors
Representatives from the UK, US, Australia, Canada, and New Zealand recently finished a two day meeting in London where the countries renewed their commitment to seeking encryption backdoors from technology companies around the world. The meetings were held by the UK’s Home Secretary, Priti Patel, and the official topics were strengthening the countries’ abilities to operate against terrorism and human sex trafficking. Both UK Attorney General Geoffrey Cox and the US Attorney General William Barr were present. That’s the same William Barr that promulgated last week that tech companies would just have to “accept” these government ordered encryption backdoors.
Governments want tech companies to build in encryption backdoors and “ghost protocol” functionality to their products
The plan to put encryption backdoors that allow law enforcement eavesdropping is called the ghost protocol by the GCHQ (the UK’s NSA).
While the meeting’s official agenda and minutes are not available to the public, the UK Home Office didn’t leave much to the imagination in a statement saying:
“We need to ensure that our law enforcement and security and intelligence agencies are able to gain lawful and exceptional access to the information they need.”
The GCHQ has specifically mentioned something called they’re calling the “ghost protocol,” which describes a fantasy scenario where police and other law enforcement officers could be surreptitiously added into supposedly encrypted group chats. Supposedly, applying a “ghost protocol” to WhatsApp was the main concern of the discussion. Besides precluding a backdoor, a world where this happens is a world where the laws of mathematics are being ignored by governments. Something that Australian Prime Minister Turnbull has actually specifically called for.
Tech companies are adamant that encryption backdoors and ghost protocols, aren’t possible, and rightly so
Tech companies continue to try and educate ignorant politicians that this is impossible to do securely, but the pleas fall seem to be falling on deaf ears. Private Internet Access continues to protest against government encroachment on tech companies and will never built in any encryption backdoors or ghost protocols. And we aren’t the only American tech company to be taking this hard stance. Apple, Google, WhatsApp, and a total of 47 other tech companies have signed a letter condemning this mere train of thought by governments.
What’s truly concerning though, is that some tech companies such as Facebook in particular, are simultaneously developing ways to screen, filter, or otherwise algorithmically “deal” with encrypted messaging. In case you’re wondering, yes that does include decrypting the supposedly end to end encrypted messaging and destroying their messaging apps’ value proposition in its entirety.
Despite this, the Five Eyes are trudging along in their quest against encryption
This meeting of the most powerful English speaking countries’ governments is a yearly occurrence known as the Five Eyes Summit and has been held since 2013 – with the last ones being held in Canada. In fact, the participating countries in these anti-encryption talks have been on this warpath for quite some time. Australia was the first Five Eyes country to pass an anti encryption law in late 2018.
The sooner the politicians in charge realize that they will unintentionally regulate the world into a more dangerous form of itself, the better. With the current path, governments will be lowering the efficacy of the encryption in every day devices and software that is used by the masses – making those popular apps vulnerable to decryption and attack by hackers by way of the exact same encryption backdoor that the government is asking companies to include. As Private Internet Access’s Derek Zimmer so concisely puts it: Government backdoors don’t work.
To put it in hip colloquialisms, the Five Eye countries need to ghost the idea of a ghost protocol and instead encourage strong encryption and provide the masses with the education on cryptography to make it effective.
Comments are closed.

We must stick to open source! They will have no ghost power then.