Why PIA doesn’t fly a warrant canary: it’s solving the wrong problem

Private Internet Access doesn’t have a warrant canary. That’s because warrant canaries alert somebody to damage that has already happened. The right way to go about the problem is to prevent the damage from happening in the first place.
At PIA, privacy is at the soul of what we do. Our business partners have occasionally been surprised when we say upfront that we’re in privacy first, business second – but that’s the passion we have. Making money is a matter of being able to continue pursuing the primary goal, privacy, on a sustainable basis.
Given this, we’re sometimes asked why we don’t fly warrant canaries on our web page: having a short statement designed to technically circumvent gag orders about what, when or where various authorities have legally coerced us to give up private information on our customers. A warrant canary can look like this:
“In 2014, this company did not receive any coercing legal request for private customer information.”
The idea is that if and when this statement disappears, it’s the equivalent of saying there were authorities grabbing what they wanted and preventing the company from talking about it – so what the company does, in order to circumvent the gag, is to remove the statement that it’s never happened.
This is going about the problem in the wrong way, when you’re a privacy company. The right way is to not have any collectable information in the first place.
A warrant canary is a little bit like a fire alarm going off. Great. You know there’s a fire. Now what do you do?
This is why at PIA, we have designed our operations to prevent this from happening in the first place. There are no logs. There is no identifying information that can be collected, regardless of the amount of force applied. There are several companies who claim they don’t log, but do anyway at the end of the day. In contrast, we have public court records to prove we don’t log anything, available for anyone to read (pages 11-12):
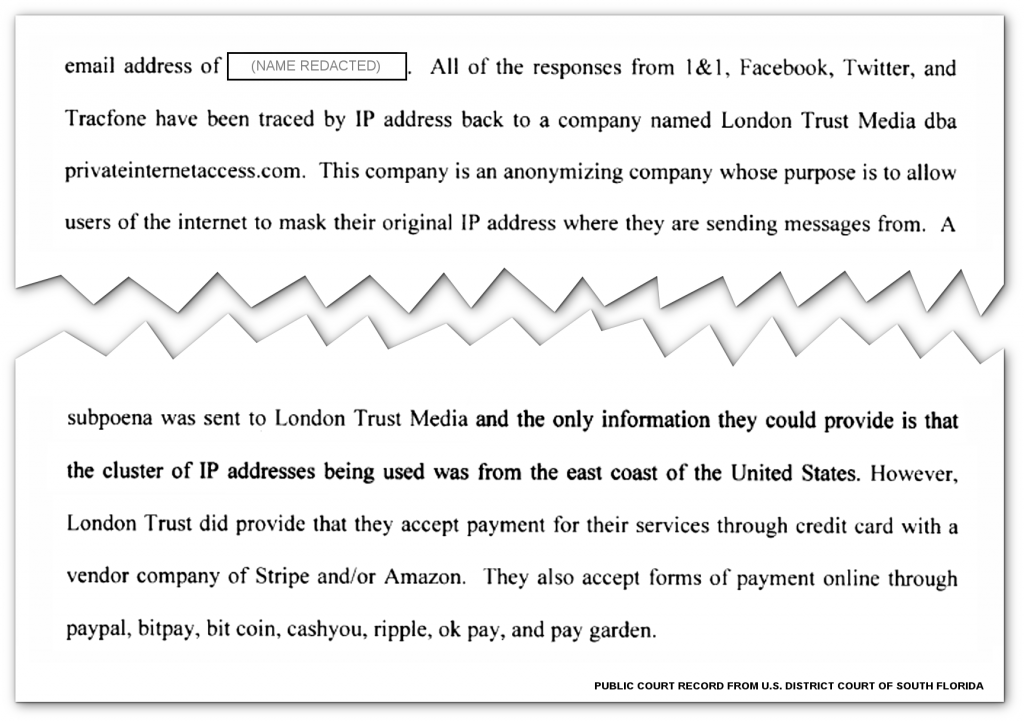
“All of the responses from 1&1, Facebook, Twitter, and Tracfone have been traced back by IP address to … privateinternetaccess.com. […] A subpoena was sent […] and the only information they could provide is that the cluster of IP addresses being used was from the east coast of the United States. However, [PIA] did provide that they accept payment for their services with a vendor company of Stripe and/or Amazon. They also accept forms of payment online through paypal, bitpay, bitcoin, cashyou, ripple, ok pay, and pay garden.”
The actual court record looks like this, with this passage divided across a page break:
So with nothing logged that can identify our users, and public court records to show for it, the question remains what to do if PIA is coerced into logging – or rather, if authorities try to coerce PIA into something like that, such as was the case with Yahoo recently, when the NSA had forced it into spying on its own users.
There is a precedent for this, and it is Lavabit choosing to shut down operations instead of selling out its users (specifically, selling out Edward Snowden). That’s also exactly what Private Internet Access has already done once, when Russia demanded that we start logging our users’ identities, after seizing PIA servers.
Our response was to immediately shut down operations in Russia:
The Russian Government has passed a new law that mandates that every provider must log all Russian internet traffic for up to a year […] Upon learning of the above, we immediately discontinued our Russian gateways and will no longer be doing business in the region.
And this, in summary, is why Private Internet Access doesn’t use warrant canaries.
Comments are closed.

I’ll have to disagree with you Rick on this one. Going back to your fire alarm analogy, it’s better to prevent fire and then also have fire alarm just in case rather than doing everything you can to prevent fire, then have some lost spark make it anyway and burn your house down.
What I mean is that you should do both.
That is interesting! If you do not log , how were you able to handle the cluster of IP addresses?
The DHCP server maintains a table of who has what lease right now. We just stopped logging who used to have a lease in the past. That log was mustly usefull to the DHCP developers when initially debugging the program, not the folks running it. Unnless they hit a bug, of course! Then we can turn it on again for a while.
Even this could be problematic? What if I begin an openvpn session with PIA and then for days on end keep it running (as I usually do) with the same lease being renewed? If authorities or others asked for the current live information relating to an IP address?
Well, this was at York and/or Geac and if we were served with a court order before the end of the lease, we’d have little choice but to provide the information we did have. I can’t speak about PIA (;-))
I was wondering the same. If PIA did not log, how did they know a cluster of IP addresses were from east coast?
I am curious though, what if the PIAs local government forces it to start logging secretly? What than? The whole thing just shutting down like Lavabit seems unimaginable.
They’re in 24 countries, some conveniently close to each other. I’d speculate a shift of headquarters would be in order (;-))
Many years ago at York University, the DHCP team asked the librarians what privacy considerations we should be aware of. They said “don’t ever keep any identifying information any longer than finances demand. As soon as a book is returned (or lost and paid for), the record of who borrowed and which book it was is expunged. Only statistical information is kept, like how many books were borrowed and how many times Lady Chatterly’s Lover circulated.” As we didn’t bill our students for IP adresses, we found we merely needed to refrain from logging who got a DHCP address from us. All done!
Yes, this; this is exactly it.
It’s noteworthy that the Warrant Canary was originally devised by librarians as a defense against FBI warrants, when agents wanted to see the borrowing history of a certain individual.
But today, we’ve arrived at the point where the only safe recourse is to purge any records the second you don’t absoutely need them for operations.
In a subsequent life with a software company that did library systems, I found the whole industry preferentially followed German law, which prohibited retaining circulation records. If anyone asked, the reply was “that’s illegal, we’re not allowed to do that for you”.
“…loves good whisky and fast motorcycles.” Hopefully not at the same time! This is why I love & use PIA (the privacy, not the whiskey & motorcycles).