Firefox Hardening Guide 2018
Purpose:
This guide shows a user in an easy-to-follow way how to improve the privacy and security settings of Firefox, which, when combined with a privacy VPN, gives a user a strong framework for protecting their information.
This guide is broken down into sections, each addressing different areas of security and privacy settings within Firefox. It should also be noted that these settings will break some websites, especially the components that block scripts. These problems will improve over time as the sites that you routinely visit will be fixed by your settings changes in the recommended plugins. Some websites are enemies of privacy and will not be usable securely or privately due to security flaws that break functionality or intentional blocking by the websites that cannot track you.
Also, when Firefox installs updates, it is common for some of these settings to revert back to their defaults. When Firefox notifies you that it has updated, it is a good idea to review this guide again and make sure that no settings have changed. This page will also be routinely updated with the latest information, so it is good to check this page for updates.
Update: Nov 14th 2018 – Mitigation for the SuperCooKeys privacy flaw in TLS 1.2 and TLS 1.3 added.
2018 Firefox Hardening Guide Navigation
- Section 1: Privacy Add-ons/Extensions for Firefox Quantum
- Section 2: Options in Firefox Quantum to Improve Security and Privacy
- Section 3: Advanced privacy and security improvements with about:config settings changes
- Section 4: Editing Trusted Certificate Authorities
Section 1: Privacy Add-ons/Extensions for Firefox Quantum
Block ads with uBlock Origin – Not to be confused with uBlock, uBlock Origin is a powerful ad-blocking tool that prevents most types of ads from appearing in your browsing or streaming. Unlike Adblock Plus and other alternatives, uBlock Origin does not have a whitelist and universally blocks all of the ads that it can. It is crucial to block ads because it is a common vector for both surveillance and malware.
Block much more with uMatrix – uMatrix is a powerful and script, cookie, and cross-site request blocker. It can recognize and block tracking through media and image files, and gives you granular control over what you allow and what you disallow on a per-site basis. It is important to block scripts and XHR requests as they are the most common attack vectors for malware and intrusion. We have an easy uMatrix guide here!
Block behaviorally with Privacy Badger – extensions like Disconnect and others block cookies by comparing the cookies to known ones. The EFF’s Privacy Badger blocks cookies by tracking their behavior rather than comparing them to repositories. This allows Privacy Badger to actively block new threats as they appear, even with no frame of reference to work from.
Make sure your web is encrypted by default with HTTPS Everywhere – While the web is increasingly encrypted by default thanks to Let’s Encrypt, many sites are still unencrypted or running both encrypted and unencrypted content, either out of laziness or error. HTTPS everywhere makes sure that all of the requests coming from your browser request SSL encryption, so that if it is available, it is used by default.
Check your work with Firefox Lightbeam – Once you’ve made the changes in this guide, you can check the impact of your changes using Lightbeam. Lightbeam monitors the requests that are made when you are visiting a website and gives you a visual layout so that you can see where your data is going. We have a short LightBeam guide here!
Section 2: Options in Firefox Quantum to Improve Security and Privacy
General – No Major Changes
The built in Firefox spell checker operates using local language libraries that are built into the browser. This means that your keystrokes and what you write are not uploaded to Mozilla or any 3rd party by the spellchecker. Do note that websites can disable the built-in spell checker and use their own, like gmail. This means when you are on websites you should be aware that your keystrokes within that page can always be recorded by the site and/or any 3rd party scripts running on that site.
Home – New Windows and Tabs Should be Blank Pages – Disable All “Home” Checkboxes
Having a homepage that is not a blank page allows the site in question to know every time you’ve opened Firefox or started a new tab.
Pocket is a semi-controversial system that is built into Firefox that attempts to give users a relevant homepage without receiving any data from the user. It works by Firefox downloading a list of high quality articles from pocket servers daily, and then locally, pocket compares your browsing history against the list of articles to make relevant recommendations. This allows Mozilla to push relevant content to users without ever seeing their browser history. It also has a “sponsored article” system that shows paid-for articles alongside the high quality content. The criticisms of the system are that Mozilla gets to decide what is high quality content and what is not, and that this a way to get ads (paid content) on a user’s home page by default. While pocket doesn’t pose any blatant security or privacy risks and it is open-source, I recommend disabling it for performance reasons as well as the criticisms above.
Search – Change the default search engine to DuckDuckGo – Disable Suggestions
DuckDuckGo is a private search engine that does not store or cache user results. This means that your searches remain private and are not traded or sold for marketing or surveillance purposes. Because of the non-invasive approach of DuckDuckGo, some focused searches may not give you the most relevant results. To fix this, you can use a feature called Bangs to have DuckDuckGo redirect your search to another engine like Wikipedia or Startpage in a private way. For Startpage you do this by preceding your search in the navigation bar with a !sp. For example, if I wanted to search for information on Alabaster and use Startpage through DuckDuckGo, I’d type:
!sp Alabaster
And I’d get a private Google search result from Startpage.
Search Suggestions is a feature that tries to predict what you’re typing in the search bar and provide you with relevant results before you finish typing out your search. It does this by analyzing your keystrokes in real-time through an interactive service. This means that the search provider is getting all of your information on keystrokes that type into the bar as soon as you hit the spacebar, not when you complete typing your search. This isn’t a huge privacy concern unless you leave a non-private search engine as your default.
Privacy and Security
Do not save passwords or autofill – Both of these store information that can be exfiltrated from you.
Do Not Store History as it can be pulled by plugins and shared.
Do not allow 3rd party cookies as these are nearly exclusively used for tracking.
You should leave first party cookies enabled because this gives you the option of allowing a cookie for a specific site with the uMatrix plugin. This corrects a lot of site-breaking issues for sites that you frequently visit in which specific cookies are okay.
Do not allow any suggestions in the search bar, as these broadcast your activity to 3rd parties.
Tracking protection can be enabled, but it is handled by addons as well, so it is redundant.
Block popups because not only are they annoying, but also because they are a common method of delivering malware payloads through malicious pages.
You want Firefox to warn you when sites try to install addons, as these have all kinds of security and privacy consequences.
Accessibility services are typically used in surveillance plugins for corporate networks and privacy unfriendly addons for Firefox, they should be disabled.
Do not share telemetry data with Mozilla.
On Blocking Dangerous and Deceptive Content – There is some false information circulating around in other guides about how this feature works in Firefox due to confusion about Google’s SafeBrowsing initiative. Google has two different methods of doing safe browsing, one is private and one is not. The Lookup API is the non-private method of checking URLs. This sends queries to Google servers every time you browse to a site to check if they are “safe.” This essentially hands Google all of your browsing information. The second, safer method is called the Update API. This stores a list of unsafe sites and domains locally, and you download a list from Google periodically that updates this list of domains. This method does not give Google any information from the user and it is what Firefox uses. You DO NOT need to disable this feature for privacy reasons and it does generally boost your security by checking your browsing against the blacklisted sites.
Special Section for Trusted Root CAs
This section is revisited in detail at the end of this article.
Firefox Account
Synchronizing your account across multiple devices has multiple privacy and security risks that should be avoided. Do not sign in to a Firefox account.
Section 3: Advanced privacy and security improvements with about:config settings changes
Firefox is highly configurable for privacy, and to access hundreds of advanced settings, you type about:config into the navigation bar where you normally type web addresses.
You will see a warning telling you to be careful! It is a warning worth heeding as setting things up incorrectly can make your browser crash or cause all kinds of issues. Misconfiguration can require a full reset of browser settings that will make you have to start over the process of hardening your browser.
The changes below are designed to significantly reduce the number of methods that websites can profile your activity. Why each setting is selected to be changed is included in the description of the setting.
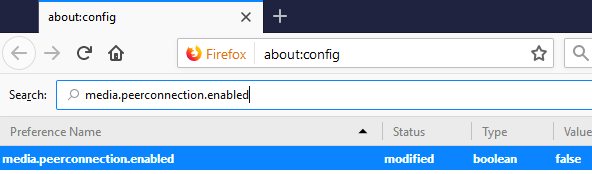
Disable WebRTC – WebRTC is a protocol related to digital rights management that helps content websites track users. It has the capability to give up your real IP address even while connected to a VPN or Tor.
To disable WebRTC, in the search bar type media.peerconnection.enabled and double click on the setting to change it to false. This disables WebRTC.
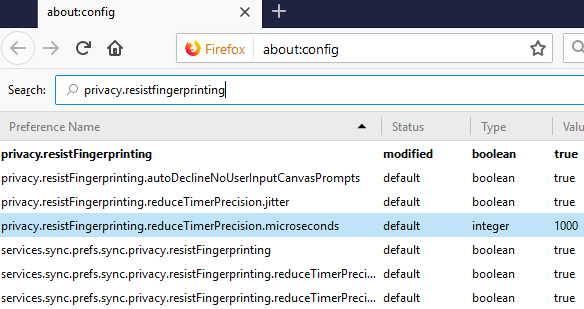
Enable Fingerprint Resistance – This setting actually manages many behaviors in Firefox, it is a group of settings that are used by the Uplift project (a sub-project of Tor) to make the browser ignore most types of fingerprinting requests.
To enable Fingerprint Resistance – Type privacy.resistfingerprinting into the search bar and double click on the setting to set it to “true.” This hardens the browser against most types of fingerprinting.
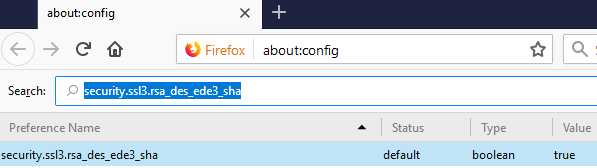
Disable the 3DES cipher – This setting allows the 3DES cipher, which has multiple known security weaknesses. It needs to be disabled.
To disable 3DES – Type security.ssl3.rsa_des_ede3_sha into the search bar, and double click on the setting to set it to “false.” This prevent 3des from being supported.
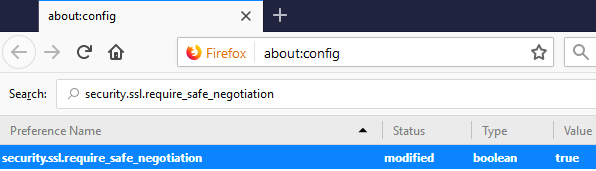
Require Safe Negotiation – This setting is for preventing a serious code injection attack related to how clients and servers negotiate which encryption settings to use. This setting forces only safe negotiation methods to be used.
To enable Require safe negotiation – Type security.ssl.require_safe_negotiation into the search bar, and double click the setting to set it to “true.” This prevents this code injection attack from working.
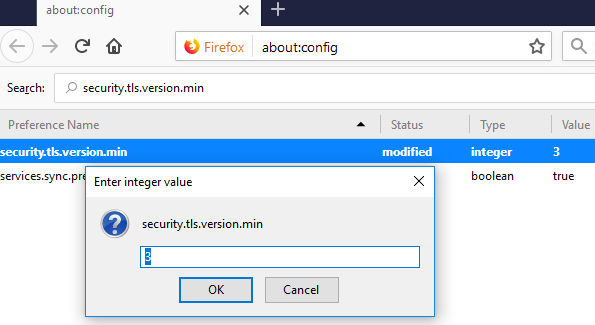
Disable TLS versions 1.0 and 1.1 – Transport Layer Security (TLS) is a protocol created by industry consensus for creating secure connections between web resources and applications. The current standard version of TLS is 1.2 and version 1.3 is rapidly being adopted at the time of this writing. TLS version 1.0 and 1.1 (1.0 esecially) have some known flaws with negotiation and cryptography in certain situations, and should be disabled for security reasons.
To Disable TLS 1.0 and TLS 1.1 – Type security.tls.version.min into the search bar, and double click on the setting. In the box that pops up, type 3 and hit okay. This will force Firefox to only use TLS 1.2 and TLS 1.3.
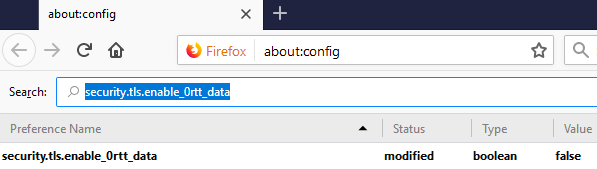
Disable 0-RTT – Zero Round Trip Time Resumption (0-RTT) is a feature that is new in TLS 1.3 that allows a client and server to negotiate a connection with fewer steps, allowing https websites to load more quickly. There are two problems with this. First, in order to do this you lose forward secrecy (generating a new key for every session and throwing away the key when the session is over). Secondly, 0-RTT requires special implementation in order to prevent replay attacks, which some web developers will certainly fail to protect from. Disabling 0-RTT enhances security and privacy.
To Disable 0-RTT – Type security.tls.enable_0rtt_data into the search bar, and double click on the setting to set the feature to false. This will force full secure negotiation for all connections made by Firefox.
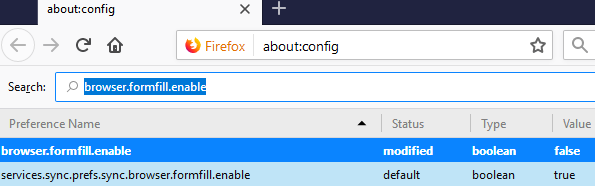
Disable Automatic Formfill – Formfilling requires that information be cached in the browser, this can include valuable information like usernames and passwords and the information can reference visited sites even with history disabled.
To Disable Formfill – Type browser.formfill.enable into the search bar, and double click on the setting to set the feature to false. This will prevent Formfill from caching any information about your browsing.
Disable All Disk Caching – Websites can write temporary information to hard drives such as access tokens, security keys, browsing data, secure scripts, and more. This information is usually deleted after a secure session is terminated, however, deleted information is trivially recoverable if it is not overwritten. Complicated firmware and drivers for flash memory based devices like SSDs introduce features like wear leveling that hide components of the storage from the OS entirely, making it very hard to verify that deleted information is actually deleted in an unrecoverable way.
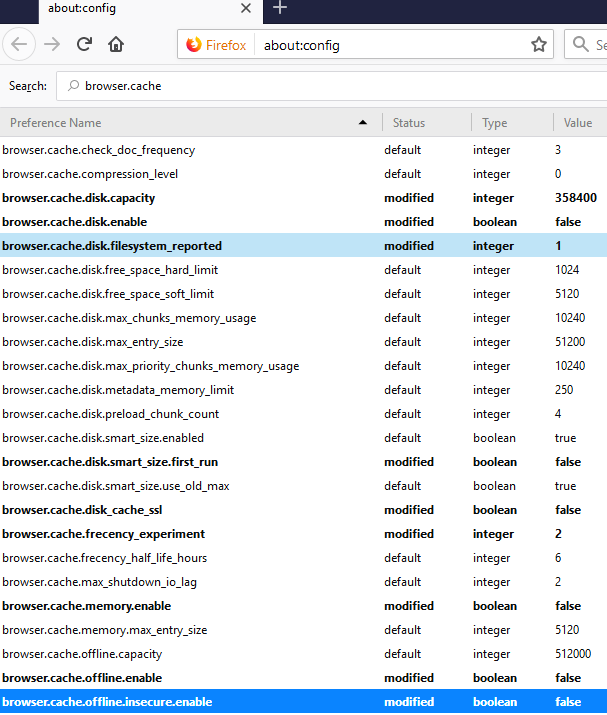
To Disable all Disk Caching – Type browser.cache into the search bar. This will pull up many settings. Look for these specific settings: browser.cache.disk.enable and double click to set it to false, browser.cache.disk_cache_ssl and double click to set it to false, browser.cache.memory.enable and double click it to set it to false, browser.cache.offline.enable and double click it to set it to false, browser.cache.insecure.enable and double click it to set it to false. This will disable all types of disk caching in Firefox.
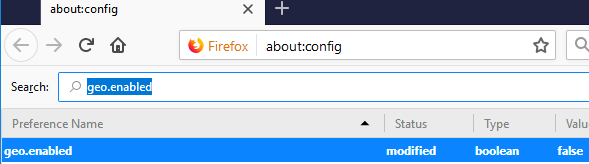
Disable Geolocation Services – Geolocation services are bad for privacy for obvious reasons. You don’t want people lasering on your exact location.
To Disable Geolocation – Type geo.enabled into the search bar, and double click the setting to set it to false. This will prevent geolocation services from working. (Note: WebRTC should also be disabled as mentioned above, as it uses a different method of generating location data.)
Disable Plugin Scanning – Plugins can query what extensions and plugins that you have installed on Firefox to profile users. Disabling this feature improves both privacy and functionality while browsing privately.
To Disable Plugin Scanning – Search for plugin.scan.plid.all and double click the setting to set it to false. This will disable the feature.
Disable ALL Telemetry Features – These are features that explicitly collect data.
To Disable All Telemetry – Type “telemetry” into the search bar. A large number of settings will pop up in the search. Search for the following and set them all to false:
browser.newtabpage.activity-stream.feeds.telemetry browser.newtabpage.activity-stream.telemetry
browser.pingcentre.telemetry
devtools.onboarding.telemetry-logged
media.wmf.deblacklisting-for-telemetry-in-gpu-process
toolkit.telemetry.archive.enabled
toolkit.telemetry.bhrping.enabled
toolkit.telemetry.firstshutdownping.enabled
toolkit.telemetry.hybridcontent.enabled
toolkit.telemetry.newprofileping.enabled
toolkit.telemetry.unified
toolkit.telemetry.updateping.enabled
toolkit.telemetry.shutdownpingsender.enabled
These changes prevent all kinds of metadata from being stored about your connection both locally and by Mozilla.
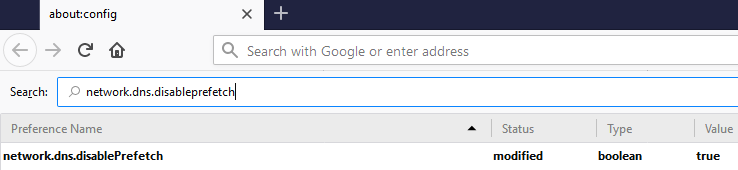
Disable Prefetching – Firefox by default will pre-load all linked pages on pages that you visit. This becomes a privacy issue because this leads to your browser broadcasting a list of the links that are on the page you are currently visiting, which can allow outside parties to profile your browsing habits from your DNS traffic, or, if you’re not on a VPN it can allow your ISP to infer what web pages you visit within secure sites by looking at the prefetch resources.
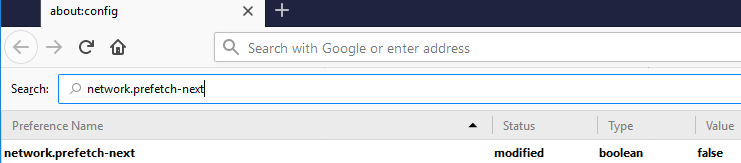
To Disable DNS Prefetching – Type network.dns.disableprefetch into the search bar and double click on the option to set the option to True. This will prevent the browser from broadcasting your browsing habits through DNS requests. You also need to disable network.prefetch-next
To Disable Network Prefetching – Type network.prefetch-next into the search bar and double click the option to set it to false.
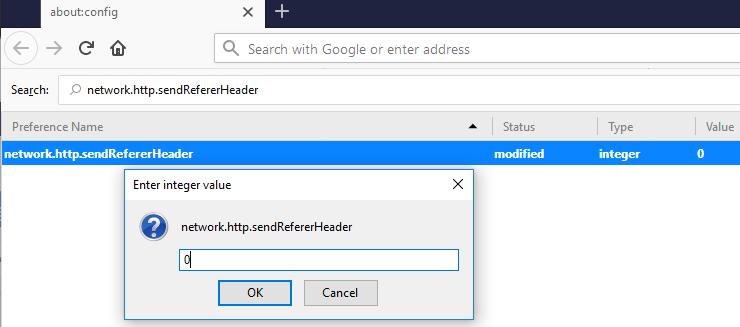
Disable Referral Headers – Websites use referral headers to track users movements from one site to another. This tells the website you are visiting what site that you came from.
To Disable HTTP Referral Headers – Type network.http.sendRefererHeader into the search bar and double click the setting which will open a dialog box. Type 0 into the box that pops up and hit okay to completely disable Referral headers.
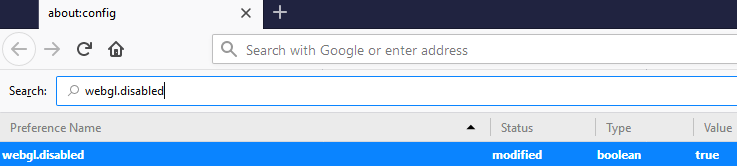
Disable WebGL – WebGL is an application interface that allows websites direct access to your graphics card. This introduces a huge attack surface for potential security risks as well as unique types of fingerprinting. It should be disabled.
To Disable WebGL – Type webgl.disabled into the search bar, and double click on the option that is displayed to set it to true.
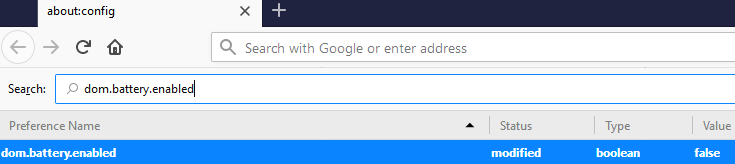
Disable Battery API – The Mozilla API can allow a site to track the current battery life of a device, which can be used in conjunction with other methods to identify and track users.
To Disable the Battery API – Type dom.battery.enabled into the search bar and double click the option listed to set it to false.
Disable web handshakes that re-use credentials – (more info: SuperCooKeys)
Disable Session Identifiers (HIDDEN FEATURE)
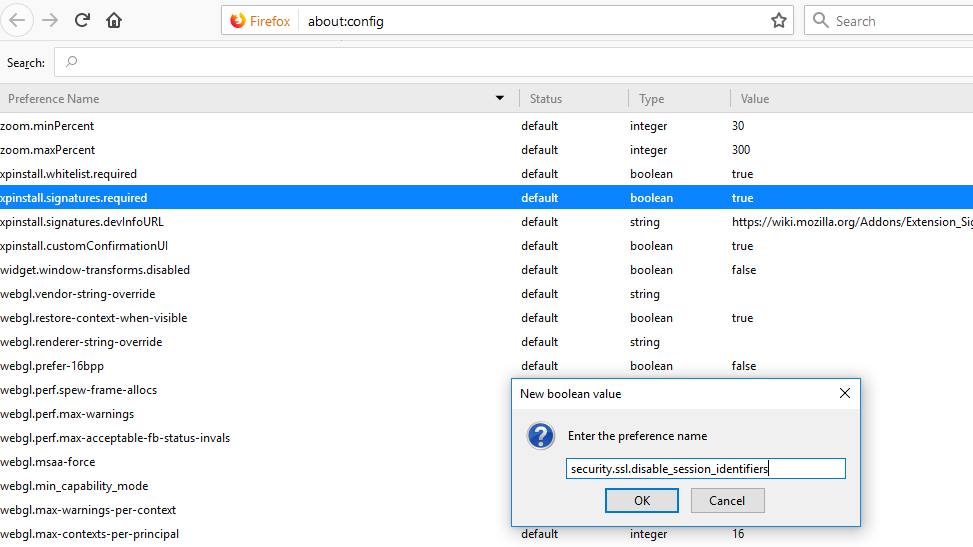
To disable session identifiers: Type about:config into your navigation bar in Firefox, in the screen that pops up, you must right click on a blank area of the page and select new -> boolean.
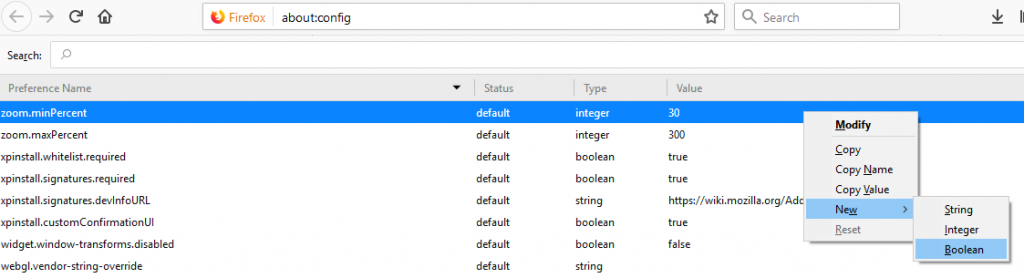
In the window that pops up, we have to enter the exact name of the hidden feature: security.ssl.disable_session_identifiers and hit OK.
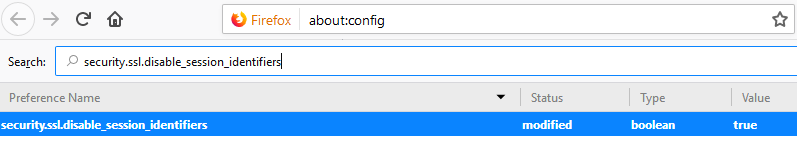
Then we have to search for the feature that we added and make sure that it is set to TRUE.
Enable First-Party Isolation
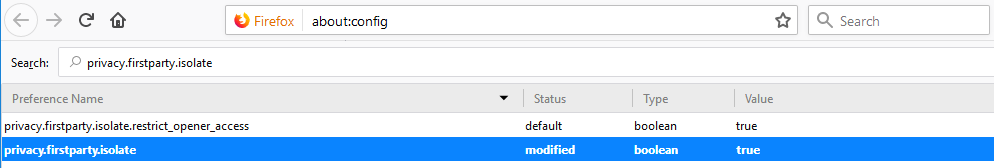
This feature prevents the browser from making requests to sites outside of the primary domain from the site. This prevents large ubiquitous services from following your keys around the web like a supercookie, and it also prevents all kinds of 3rd party data tracking.
To enable first party isolation: Type about:config into your navigation bar in Firefox. In the screen that pops up, enter privacy.firstparty.isolate into the search bar, and make sure that the setting is set to TRUE. (This setting can break websites that rely heavily on 3rd party libraries and scripts.)
Disable TLS False Start
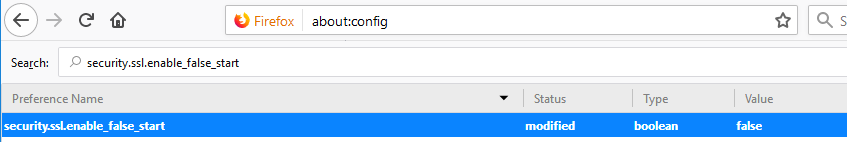
This is because it does not allow the client to fully complete its handshake before starting the actual session. There is more info here from the IETF: https://datatracker.ietf.org/doc/html/rfc7918 (See section 5. Security Considerations)
To disable TLS false start: Type about:config into your navigation bar in Firefox. In the screen that pops up, enter security.ssl.enable_false_start into the search bar, and make sure that the setting is set to FALSE.
About Camera and Microphone Access – There are many settings in Firefox related to access to the Camera and Microphone. Recently, Firefox has implemented a number of good security and privacy features surrounding access that make editing these settings unnecessary. Disabling these features in about:config will disable Mic and Camera access globally, rather than allow you to permit access to services that you want (like Jitsi Meet for audio/video chat).
If you NEVER want to use a microphone or webcam through your browser, you can manually disable access. Otherwise, you should allow your permissions built into Firefox to manage access.
Section 4: Editing Trusted Certificate Authorities
This step takes some trial and error, but dramatically helps reduce your attack surface by outside parties.
First, we need to discuss how the certificate system works. Certificates around the web tell your browser if a site is genuine and they are managed by a group of “root certificates” from organizations around the world. These organizations vouch for the security of their own root certificate and vouch for the validity of all certificates that are made from it. This means that when Typhoon (fake name used for example) creates a certificate for a website, they are telling your browser “this site is genuine because Typhoon says it is.” You are relying on the reputation of Typhoon to keep your browser safe from spoofing.
There’s some inherent problems with this system. How do we know that Typhoon’s security standards are perfect? How do we know that Typhoon would never create an invalid certificate for someone else accidentally? How do we know that Typhoon would never create a fake certificate for a law enforcement agency or spy organization?
Therein lies a large problem. Firefox (and all browsers and operating systems) trust hundreds of these root certificates by default, and for most users around the world, you don’t encounter most of these root certificates in your day to day web use.
For an example of certificate authorities that people may not want to blindly trust:
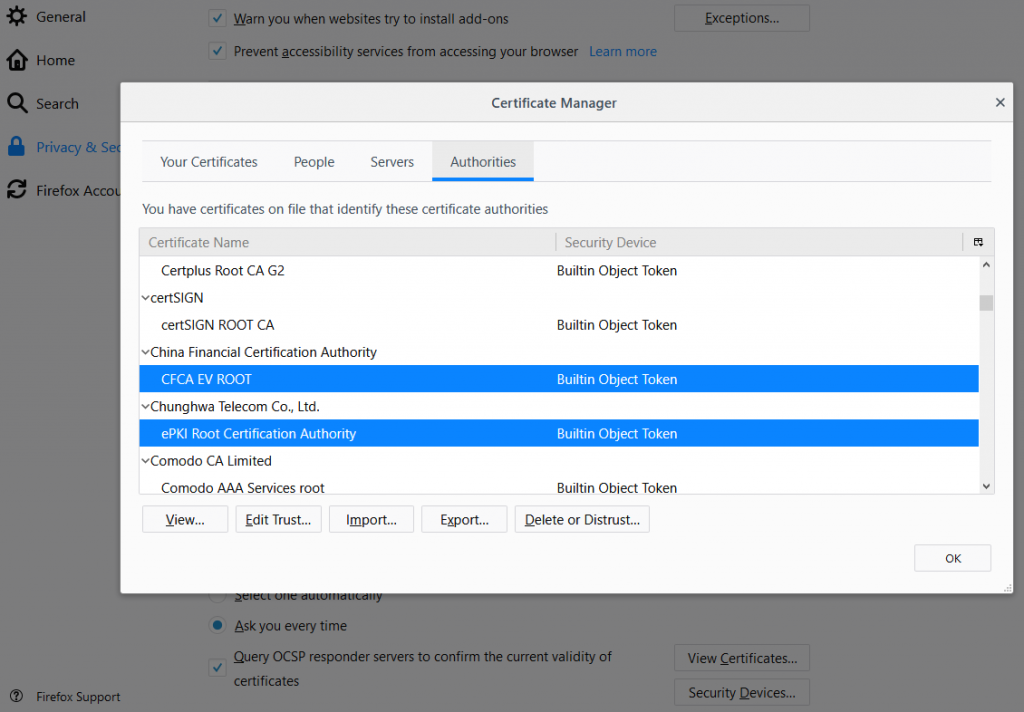
As a privacy and free information activist, I probably do not want to blindly trust certificates originating from China.
You can remove many of these root certificates from Firefox to make it so that you trust far fewer authorities. To access the certificate manager, you go to the settings menu in Firefox, and click on the Privacy and Security pane on the left side. Then you scroll to the bottom of the page and click on “View Certificates…” In the window that opens up, you can scroll through all of the possible certificate authorities and remove trust (by clicking on the Delete or Distrust… button) from all of the authorities for sites that you do not visit or do not trust for ethical reasons.
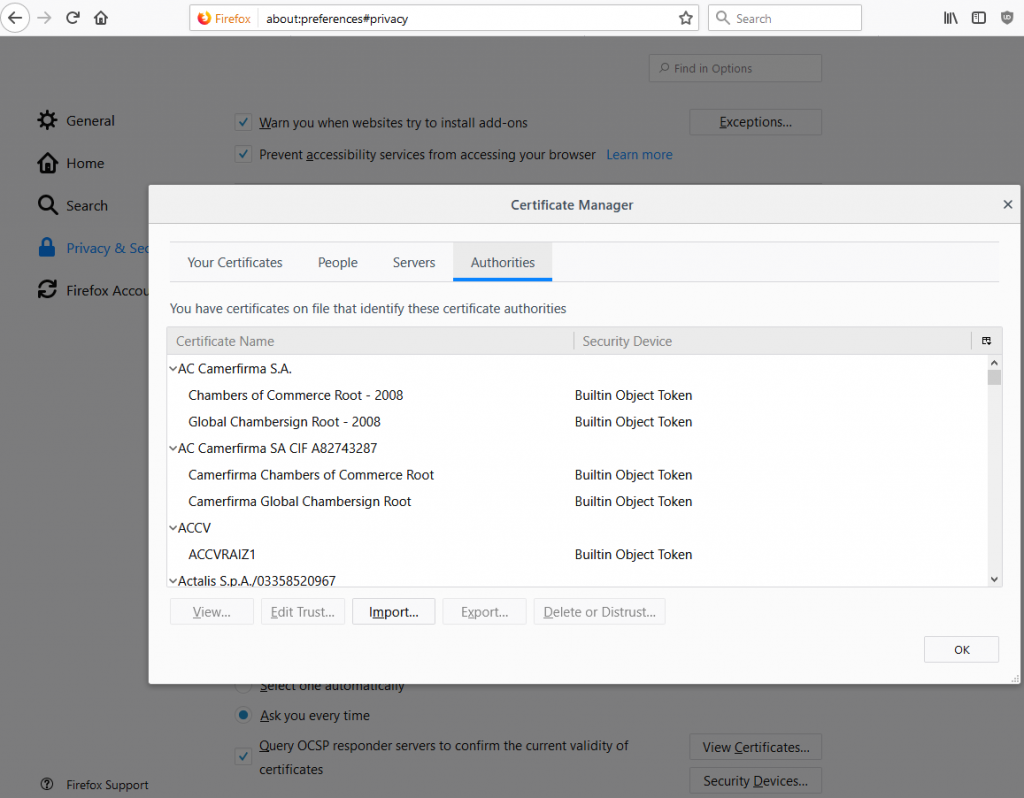
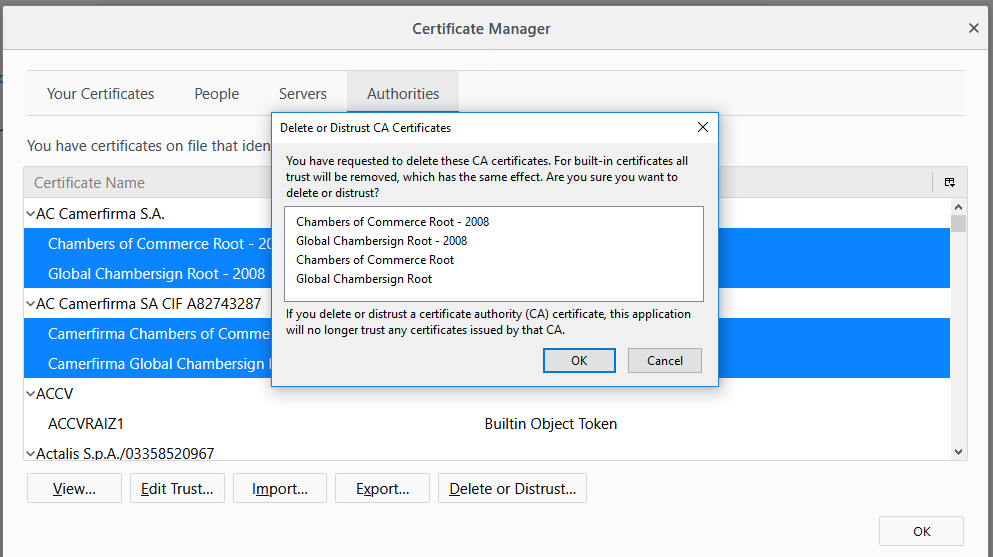
This step does require some research, you have to find out which certificates are used by the sites you visit, and limit your trusted certificates to those. Also, many of the big American certificate authorities (such as the Amazon Root CAs, DigiTrust, RapidSSL, GeoTrust, GlobalSign) will break a majority of the Internet if you mistrust them.
Personally I tend to mistrust all certificates from languages that I do not speak (which means it is unlikely that i’ll ever run into those certificates around the web) and also eliminate any certificates that cater to local regions such as Taiwan, Switzerland, the Netherlands, etc.
If you accidentally mistrust a certificate that you want to trust once again, you can click on the “edit trust” button in the certificate manager window, and check the boxes for the services that should trust this certificate authority.


